Threats on the World Wide Web
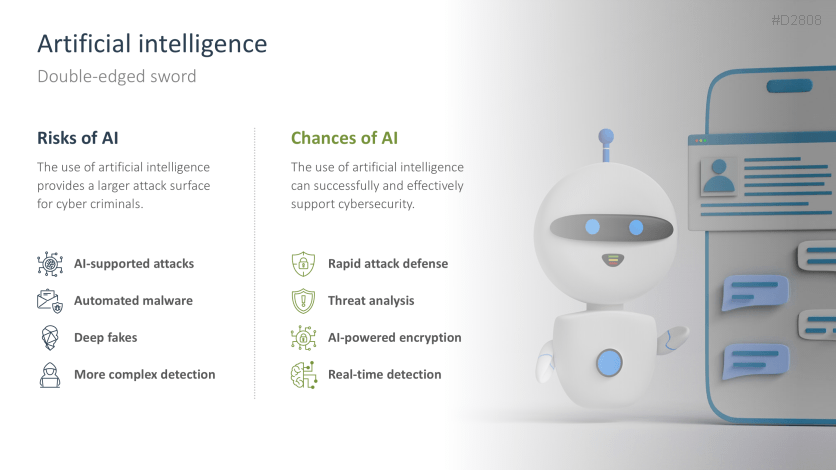
Cybersecurity focuses on the dangers and risks posed by information and communications technology. In the worst case, vulnerabilities in these IT systems can lead to sensitive data falling into the wrong hands or even being exploited for criminal activities. An effective cybersecurity strategy is needed to prevent this from happening. However, the rapid development of artificial intelligence in particular is creating new and more complex cyberattacks against which companies must take additional precautions.
Be one step ahead of hackers
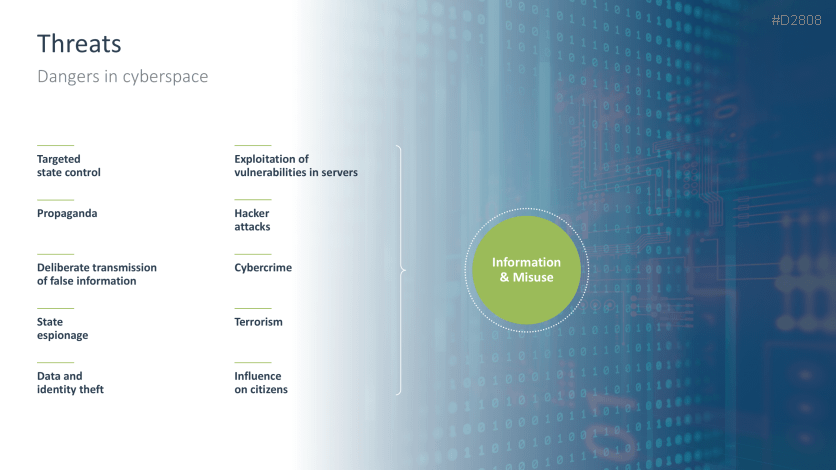
Cyberthreats are manifold: from the classic hacker, who exploits the vulnerabilities and errors of a software system for their own purposes, to programmed bots, which can move around a network autonomously and spy on data. Installing an appropriate virus scanner is a crucial step in protecting against these threats, but it's far from enough. System vulnerabilities aren't the only things being exploited. Nowadays, cybercriminals also direct their attacks against the users themselves. Whether it's phishing, spoofing or spreading malware - only those companies that sensitize their employees to threats can establish a successful and long-term cybersecurity strategy.
Cybersecurity strategies and tools
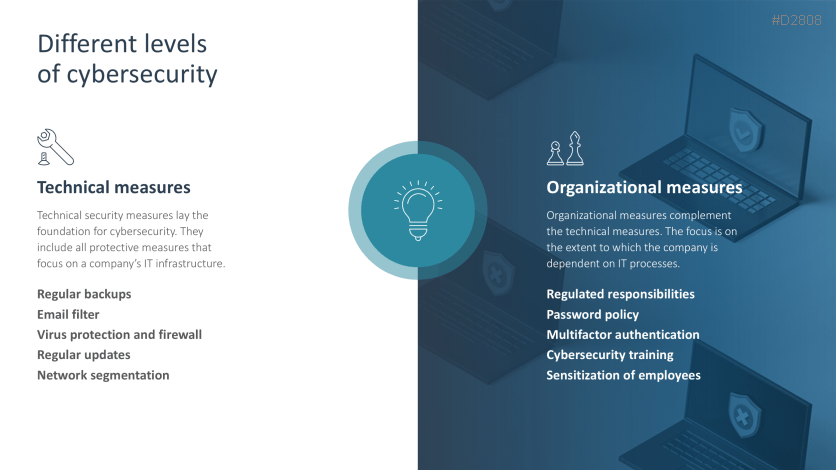
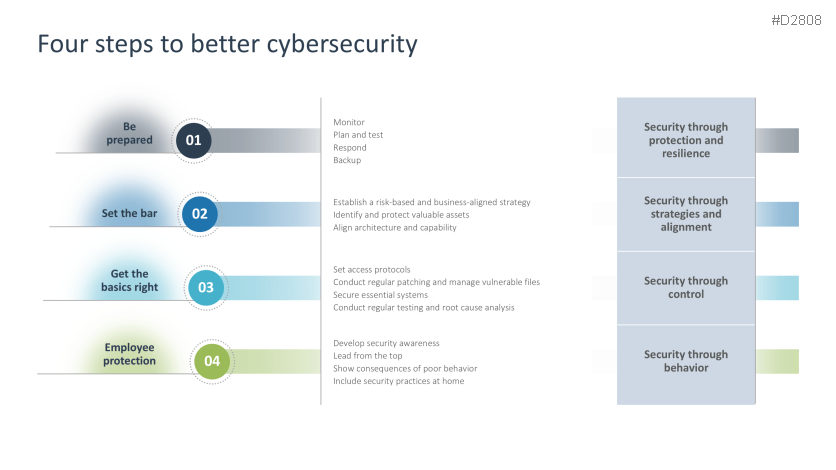
Effective defense strategies are essential in today's corporate environment. Companies can leverage both technical and organizational measures to create a comprehensive security plan. Secure IT infrastructures coupled with trained employee behavior is critical to the security program's success. Only by addressing system vulnerabilities and teaching employees how to properly handle data, passwords and sensitive information can companies successfully mitigate cyberattacks.
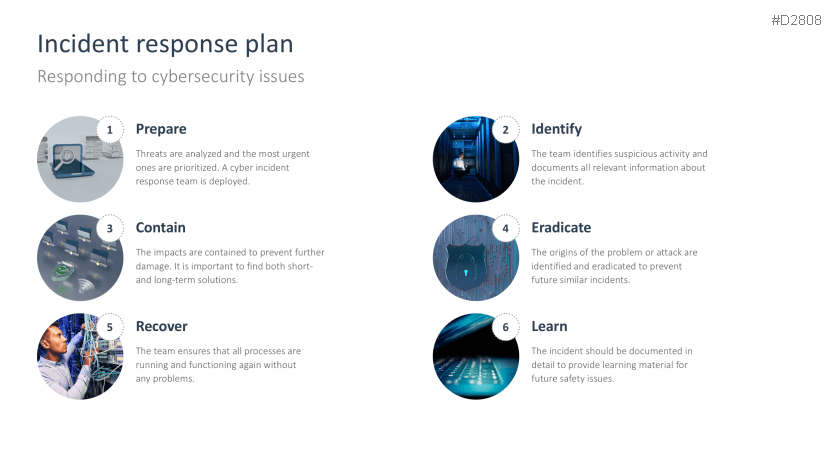
At the same time, it's also important to prepare for the worst-case scenario. No company can protect itself from all types of cyberattacks. Incident response plans document the course of action if a successful attack does occur. Only a quick and coordinated response to such incidents can minimize the impact and limit the damage.
Everything on cybersecurity in one template
Get the most pertinent information on the latest cybersecurity topics in our updated PowerPoint template. Present the current threat landscape, the role of artificial intelligence and explain to your employees the cyberattacks they can protect themselves from and how. With our template, you'll be able to create and deliver a comprehensive and engaging presentation on cybersecurity. Use our information to emphasize the importance of an effective defense strategy and illustrate what role your employees play in it.
With the Cybersecurity Template for PowerPoint, you can
- present the current threat landscape with up-to-date statistics.
- explain the most critical types of cyberattacks and corresponding protective measures.
- raise awareness among your employees about the importance of a cybersecurity strategy.
This PowerPoint template includes:
- Quote
- Why is cybersecurity important?
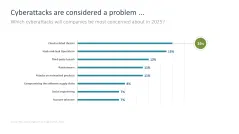
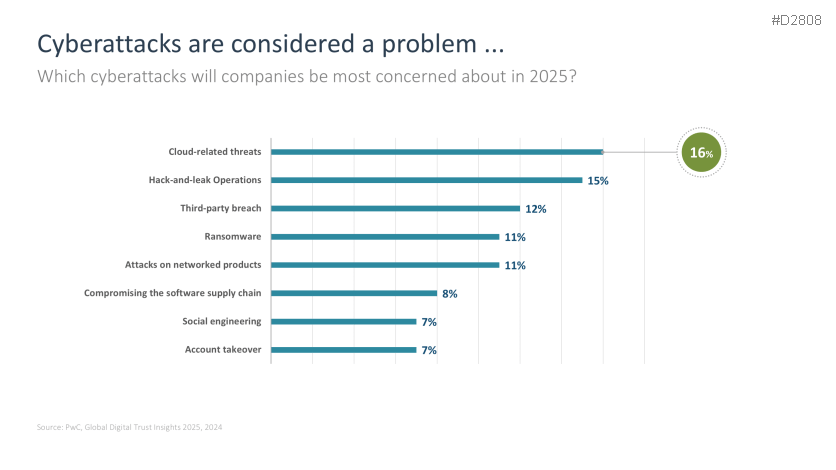
- Cyberattacks are considered a problem …
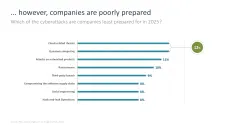
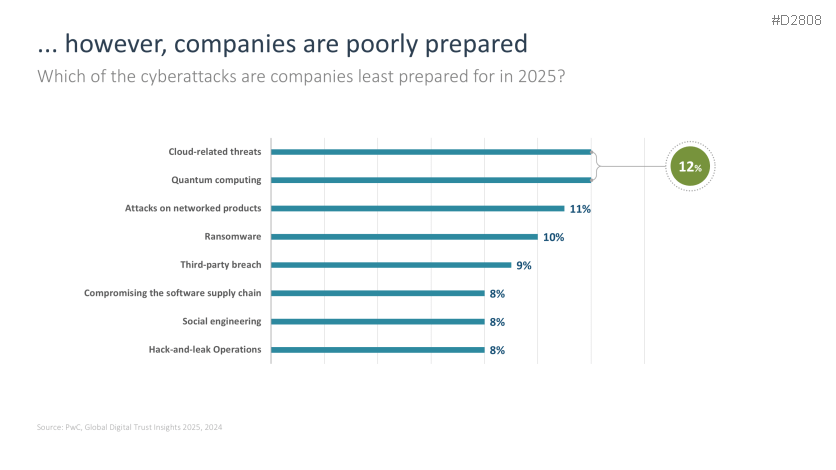
- … however, companies are poorly prepared
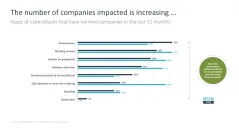
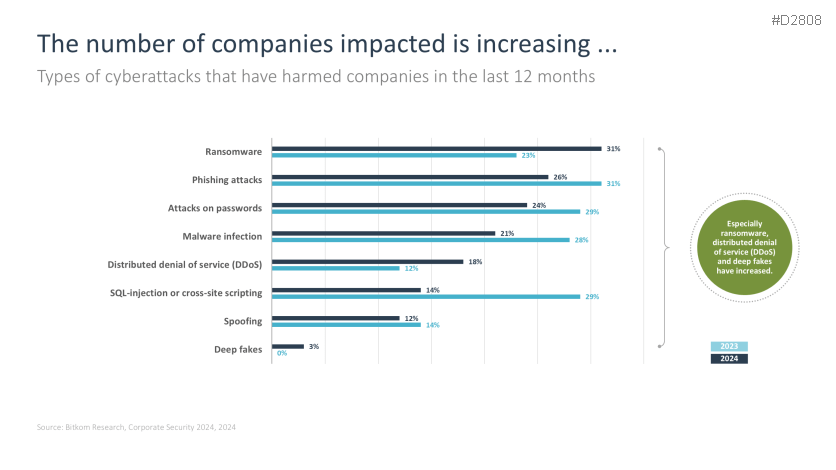
- The number of companies impacted is increasing …
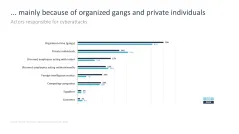
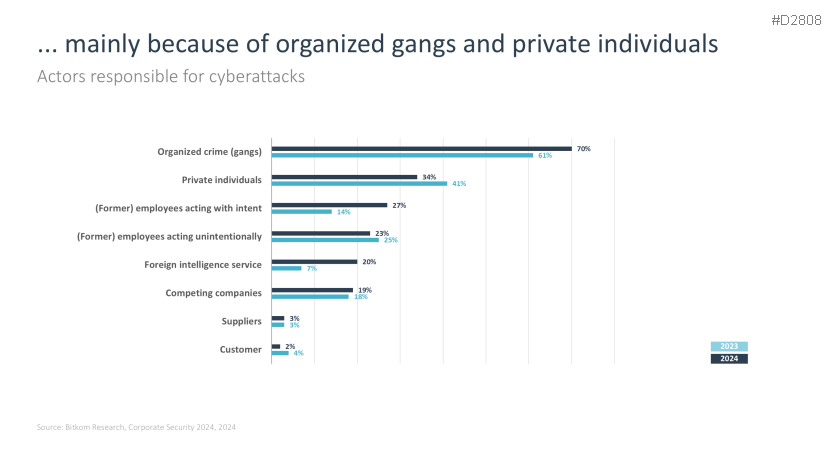
- … mainly because of organized gangs and private individuals
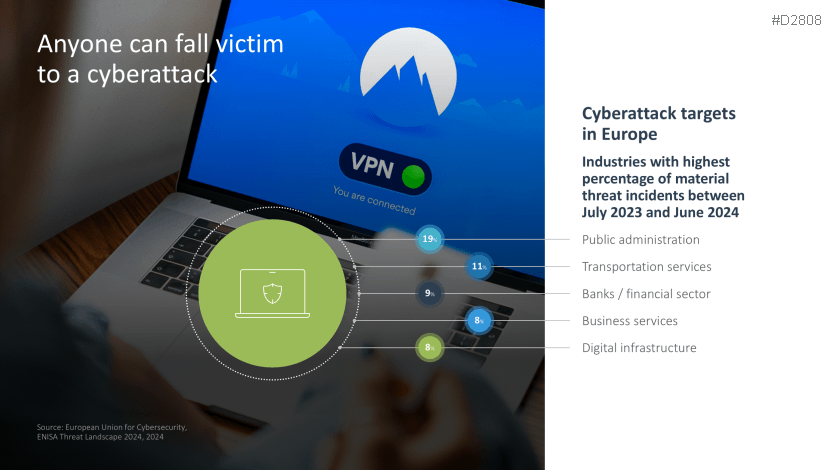
- Anyone can fall victim to a cyber attack
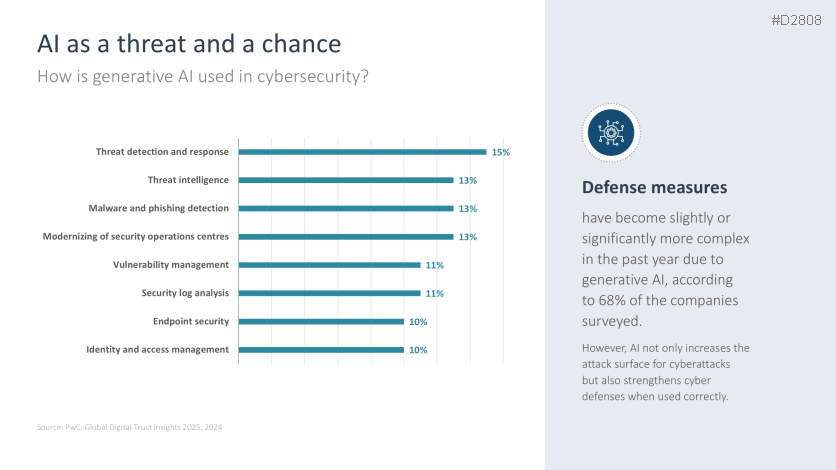
- AI as a threat and chance
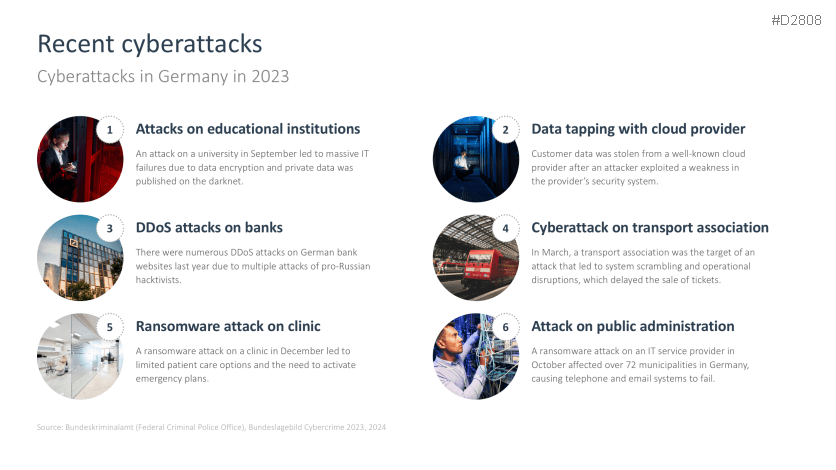
- Recent cyberattacks
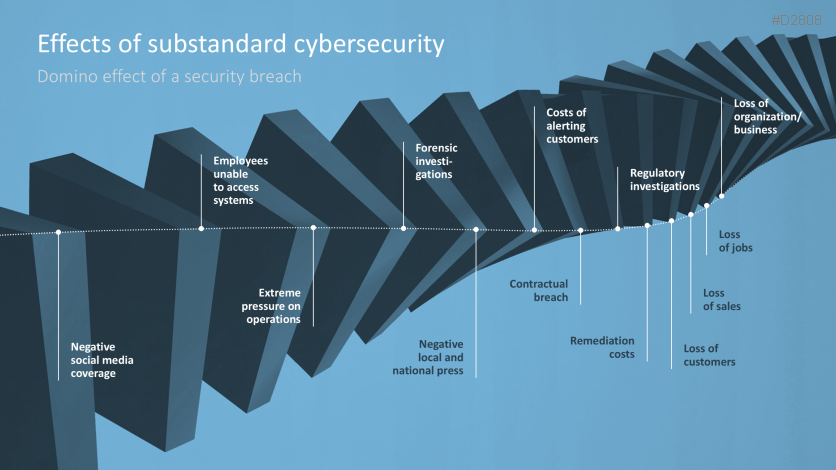
- Effects of substandard cybersecurity
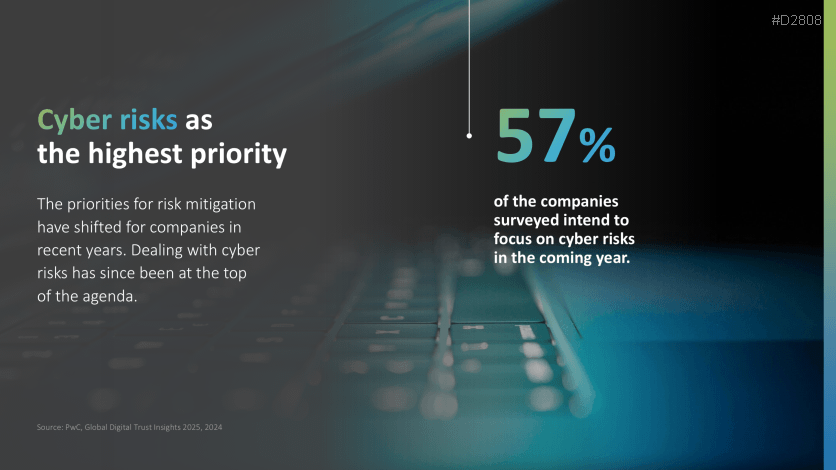
- Cyber risks as the highest priority
- What is cybersecurity?
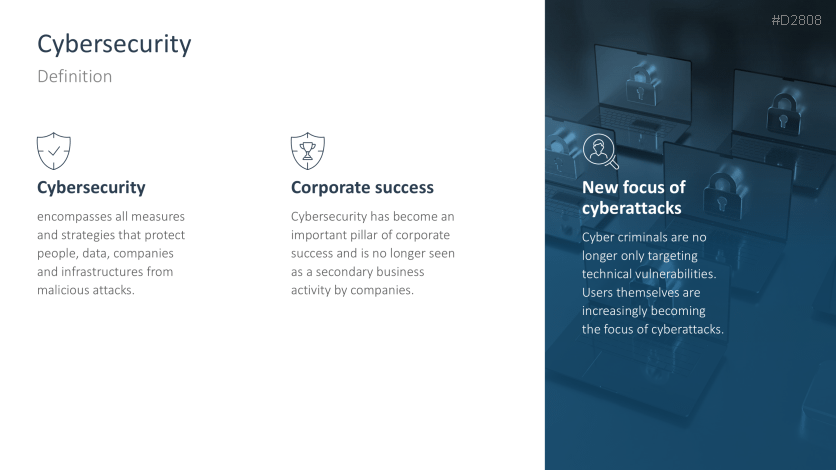
- Definition: cybersecurity
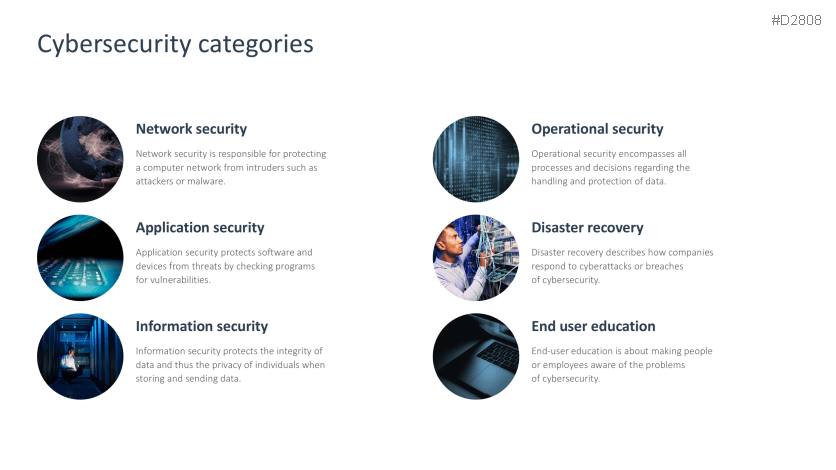
- Cybersecurity categories
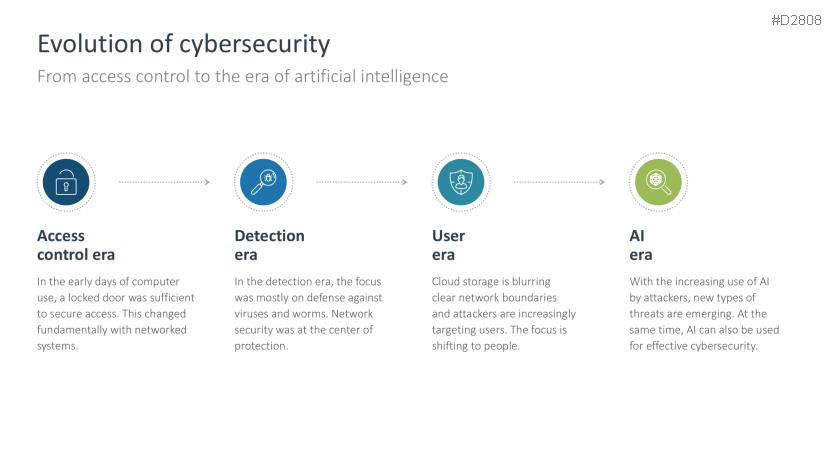
- Evolution of cybersecurity
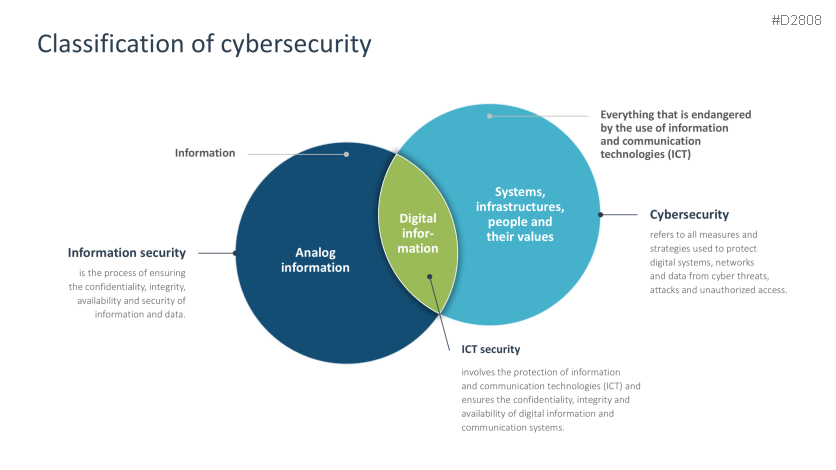
- Classification of cybersecurity
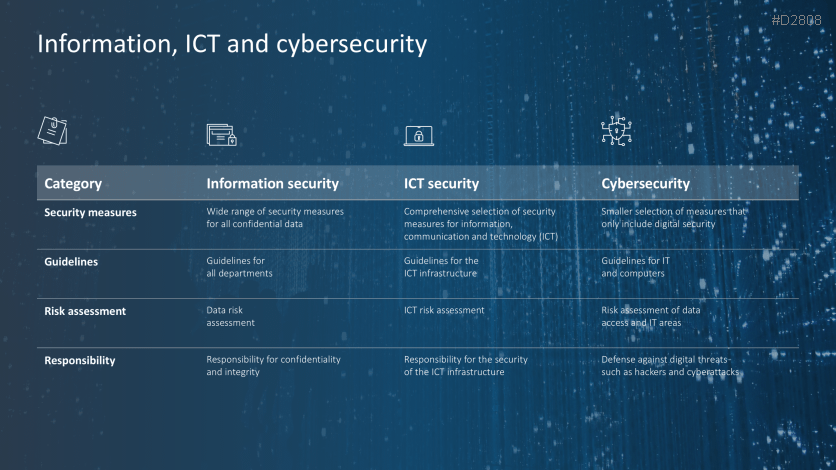
- Information, ICT and cybersecurity
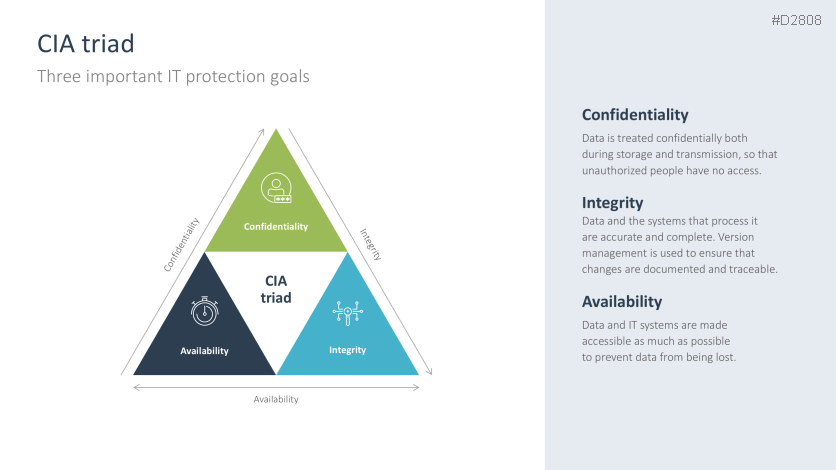
- CIA triad
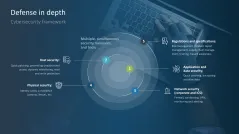
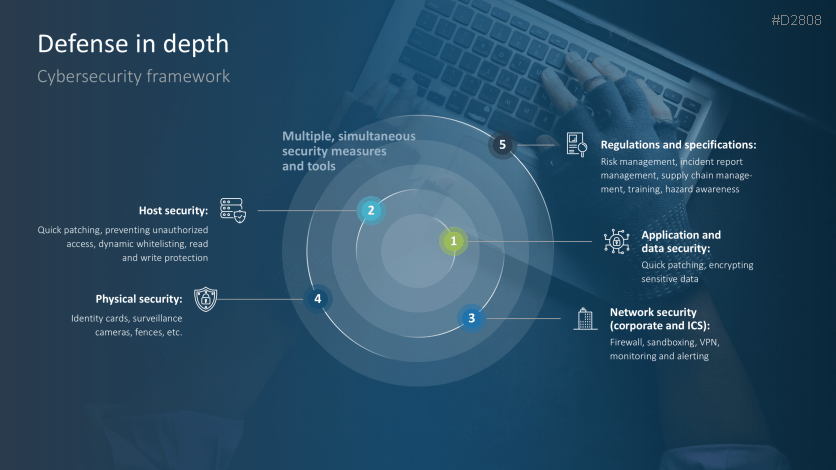
- Defense in depth
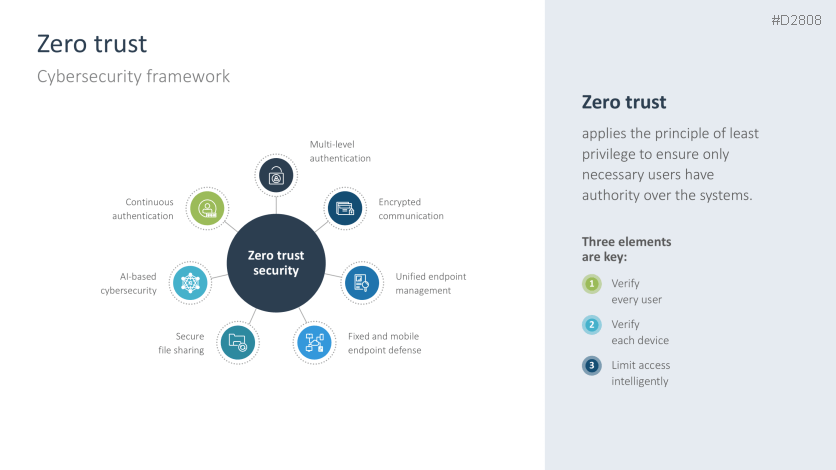
- Zero trust
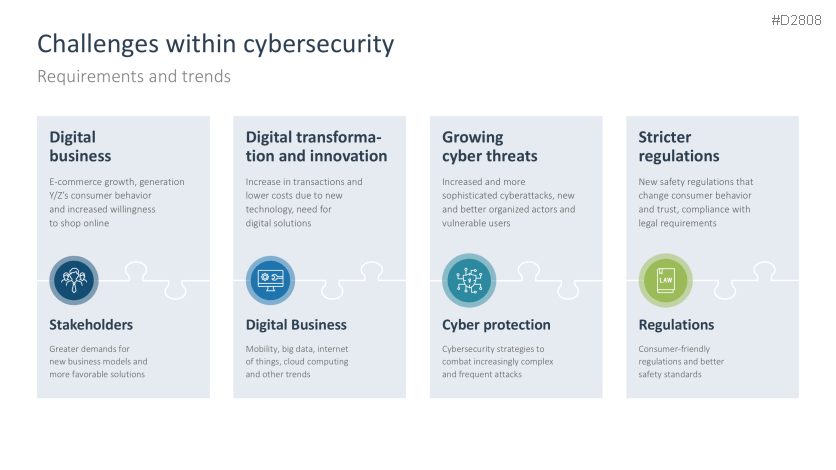
- Challenges within cybersecurity
- Threat landscape
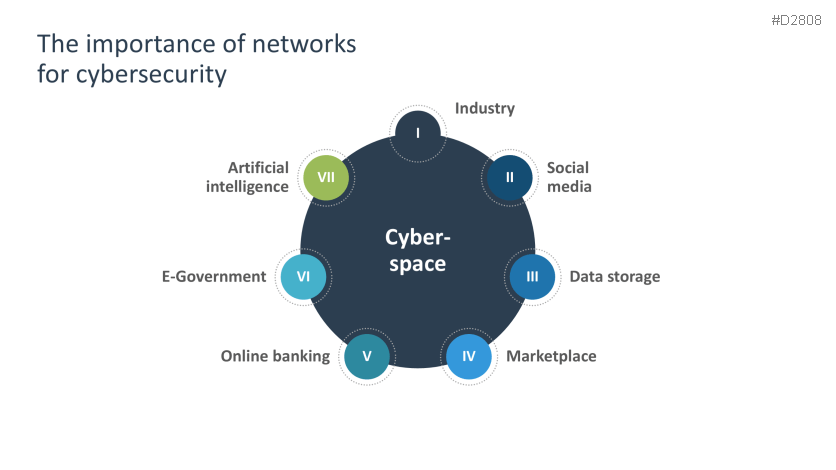
- The importance of networks for cybersecurity
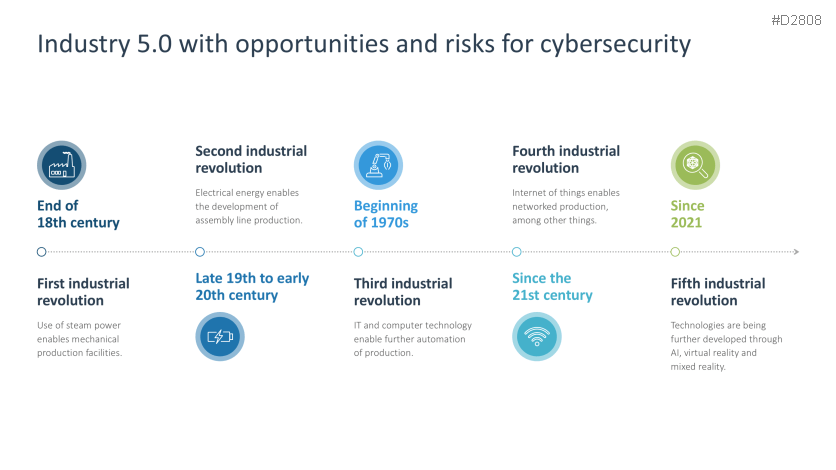
- Industry 5.0 opportunities and risks
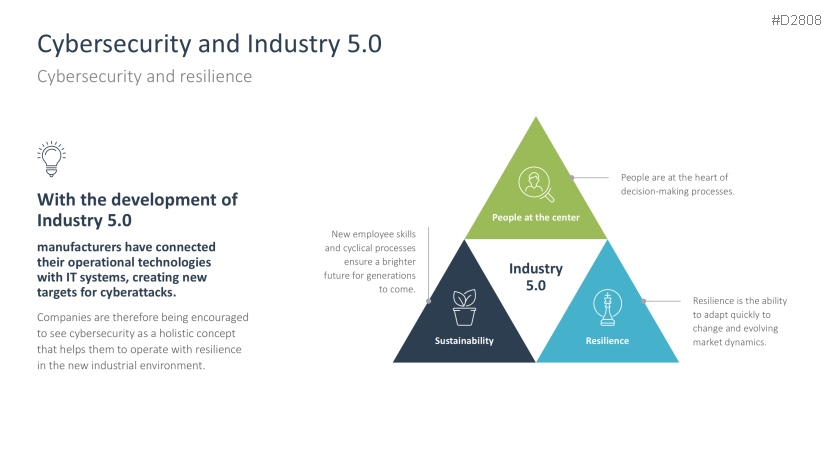
- Industry 5.0 and cybersecurity
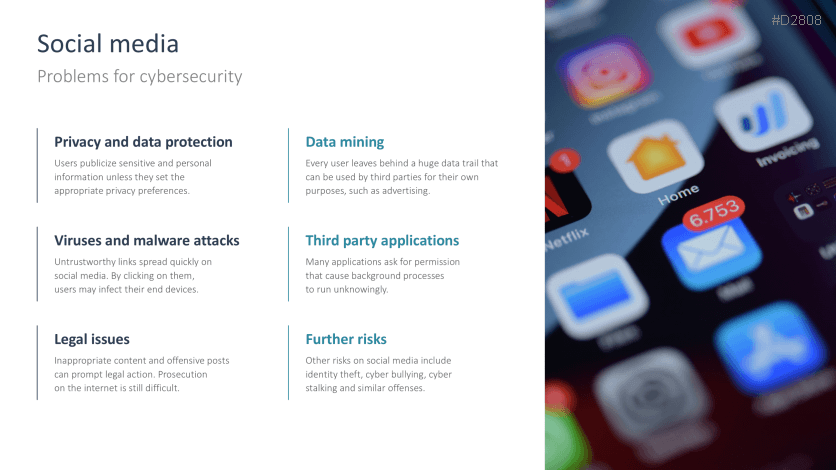
- Social media
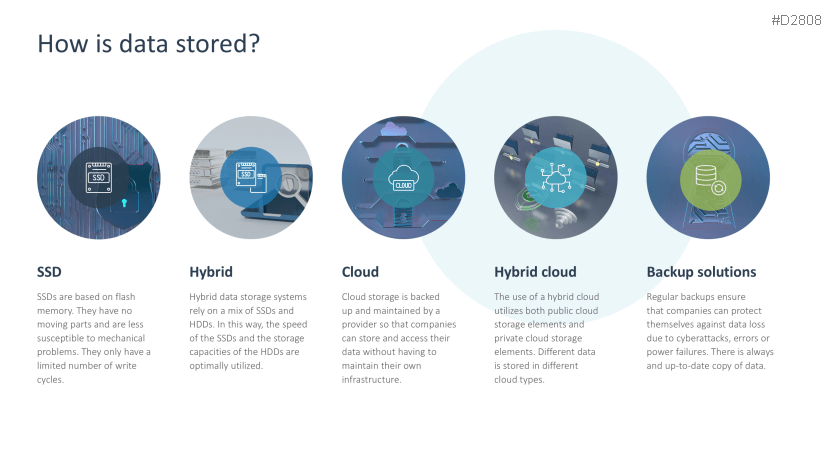
- How is data stored?
- Online marketplaces
- Future payment trends
- Online aspects of politics
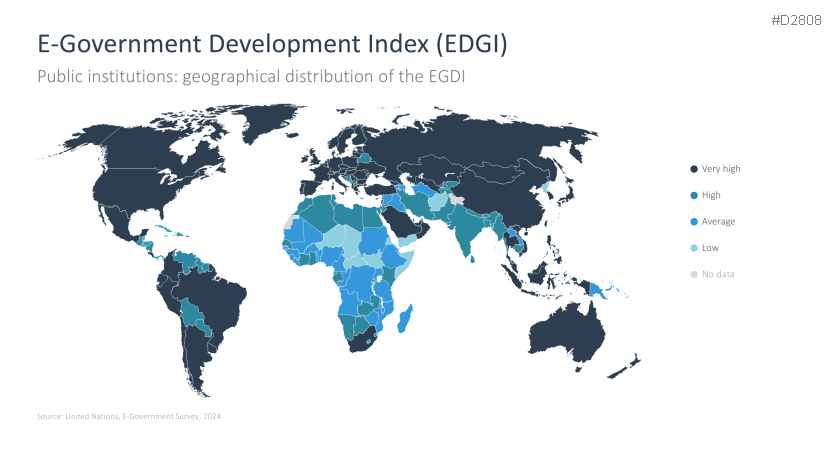
- E-Government Development Index (EDGI)
- Artificial intelligence
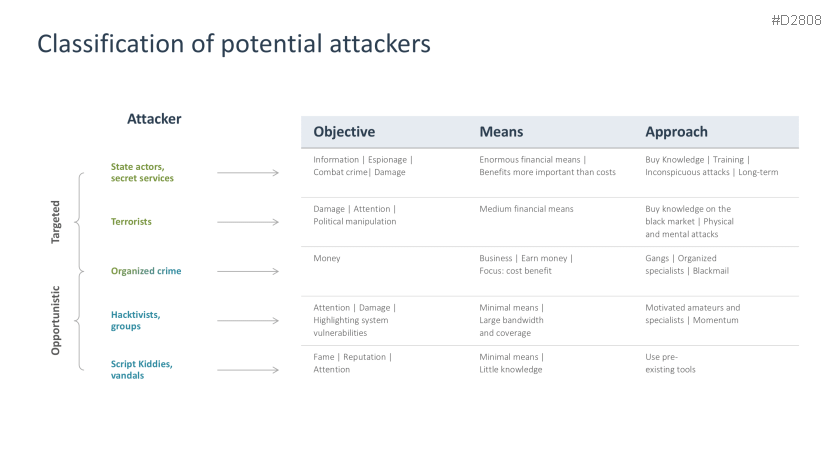
- Classification of potential attackers
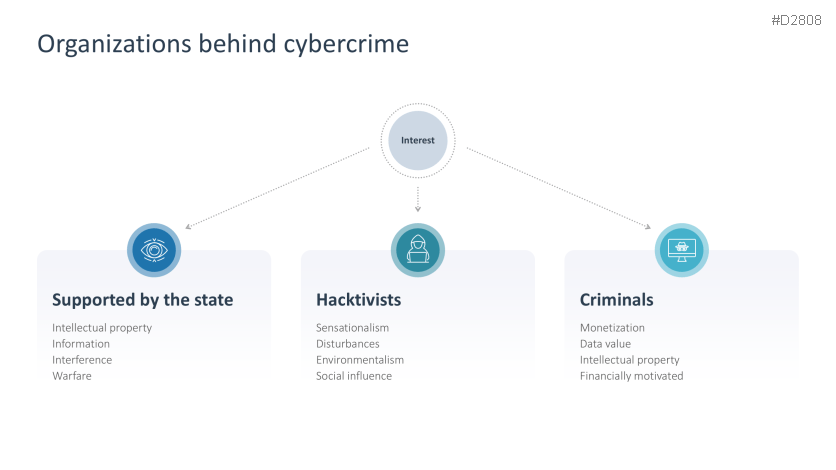
- Organizations behind cybercrime
- Threats
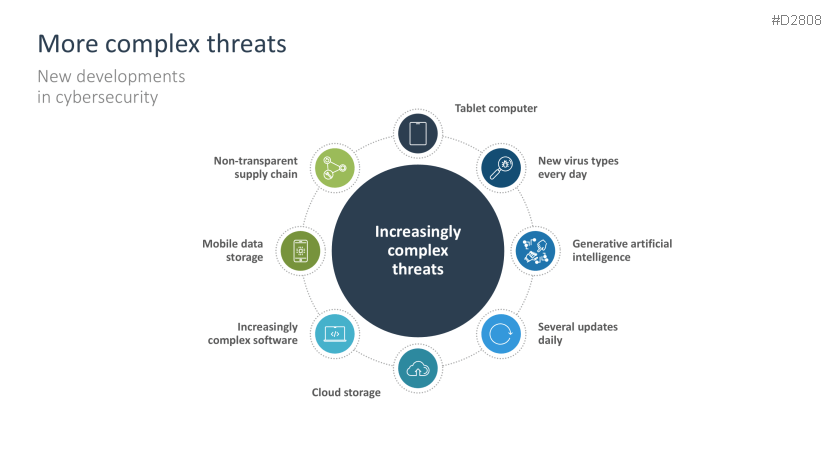
- More complex threats
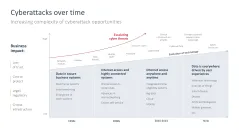
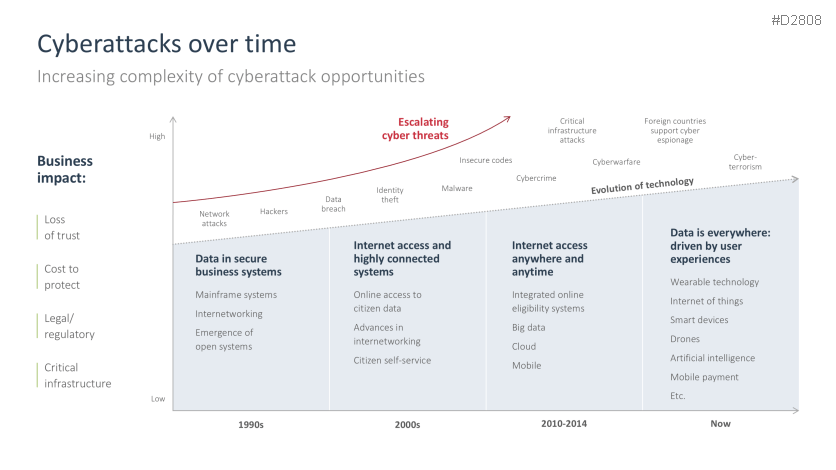
- Cyberattacks over time
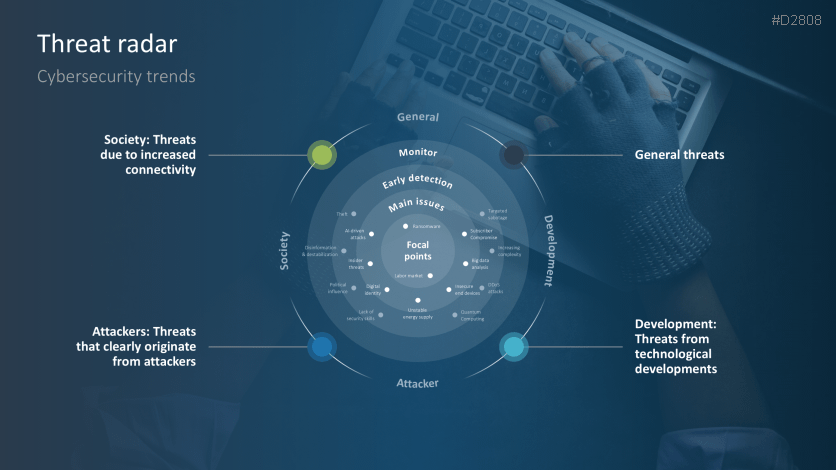
- Threat radar
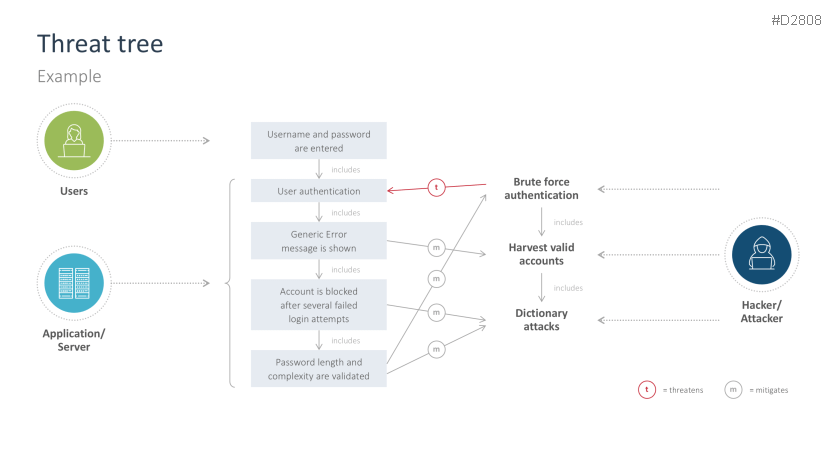
- Threat tree
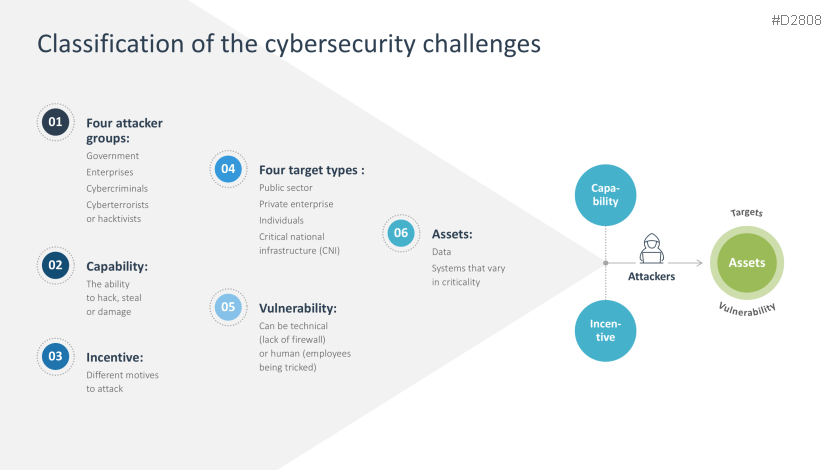
- Classification of the cybersecurity challenges
- Cyberattacks and protective measures
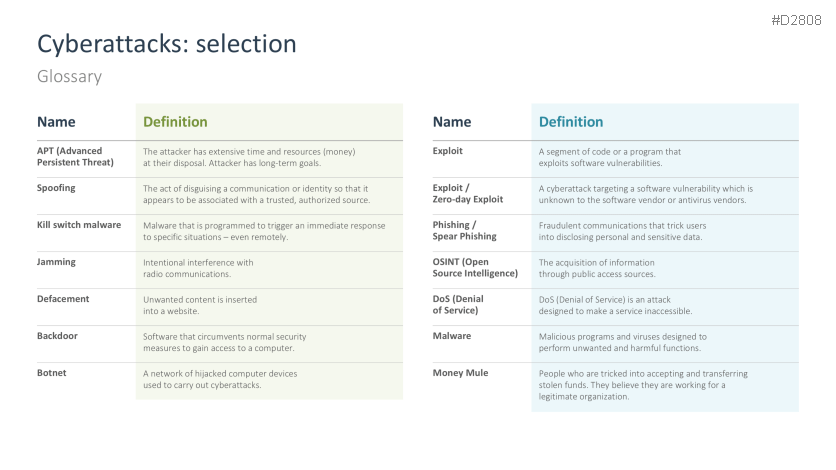
- Glossary of cyberattacks
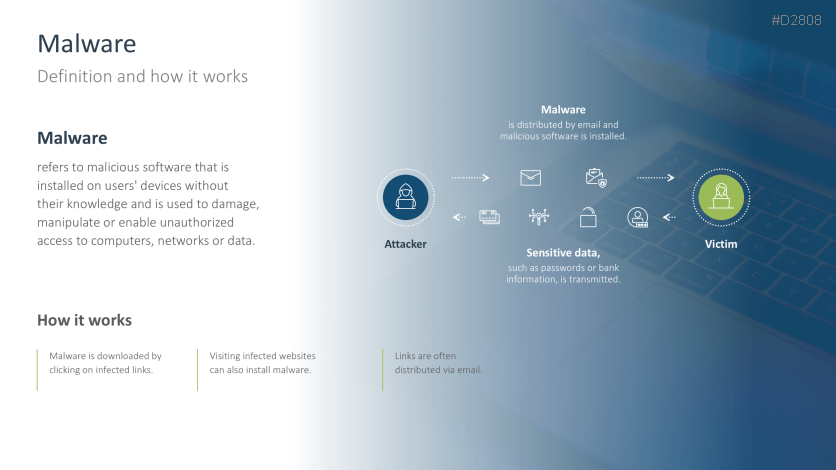
- Malware
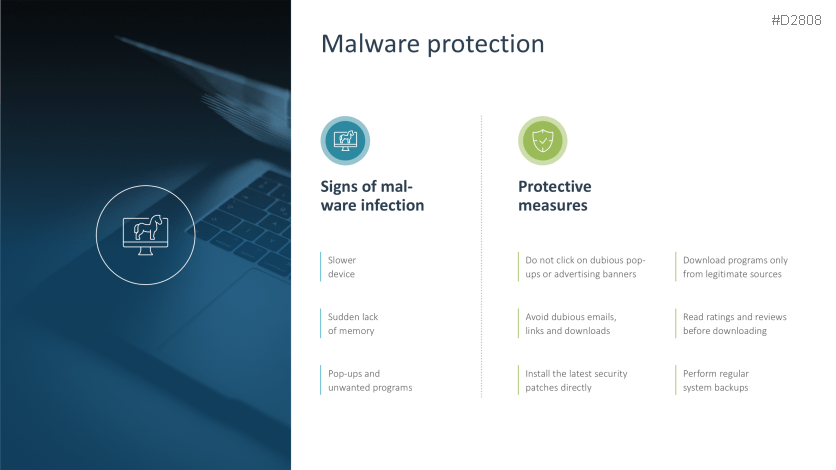
- Malware protection
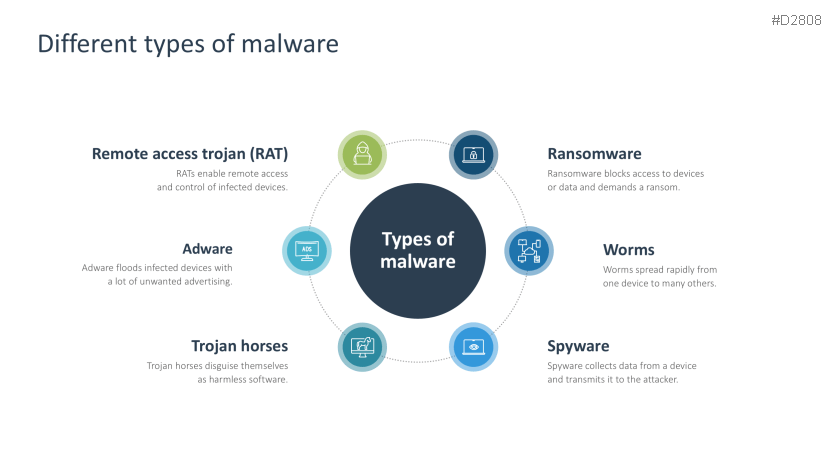
- Different types of malware
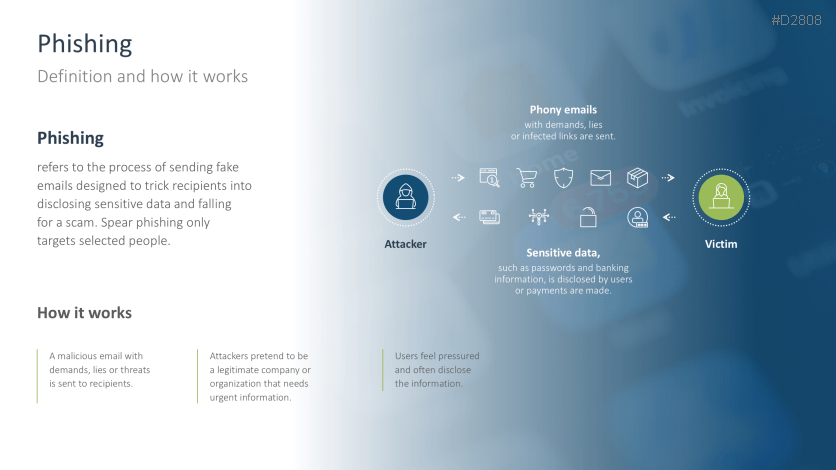
- Phishing
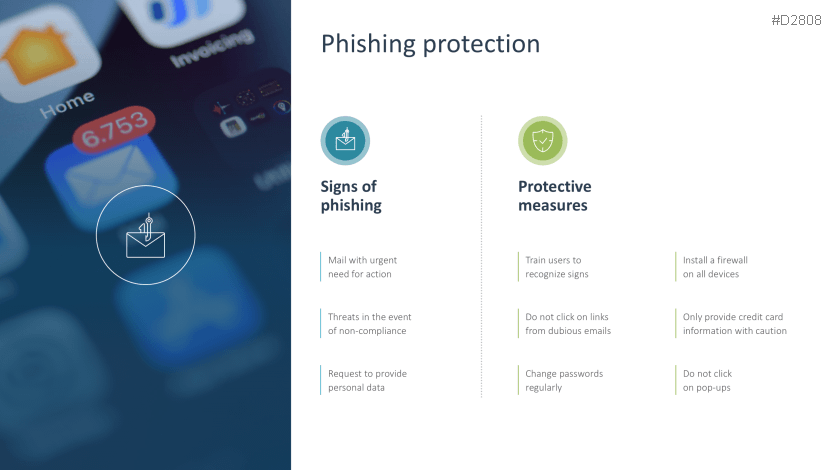
- Phishing protection
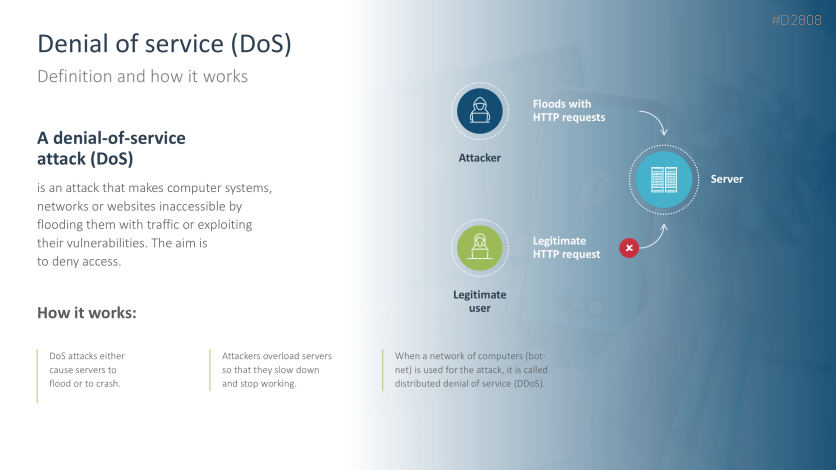
- Denial of Service (DoS)
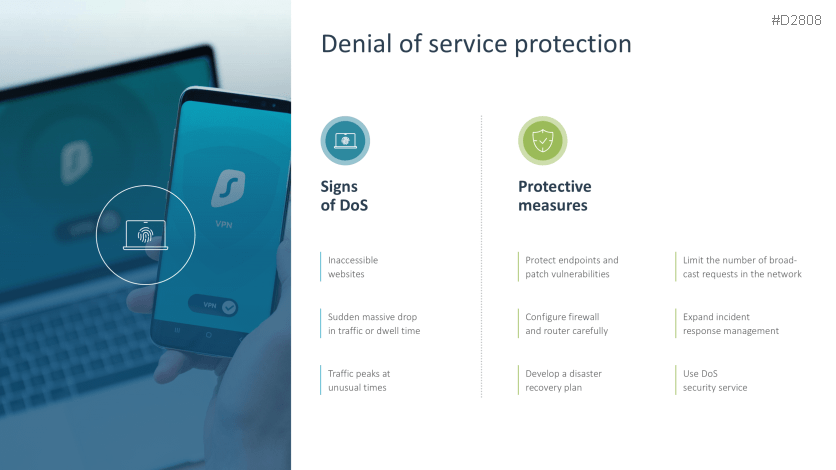
- Denial of Service protection
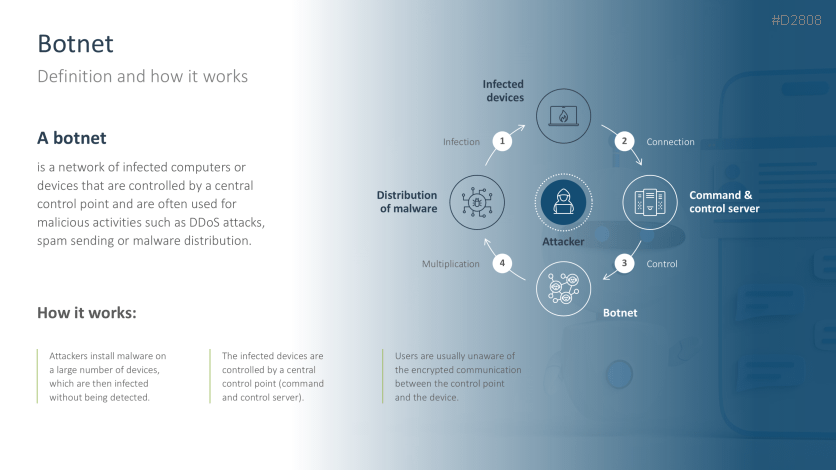
- Botnet
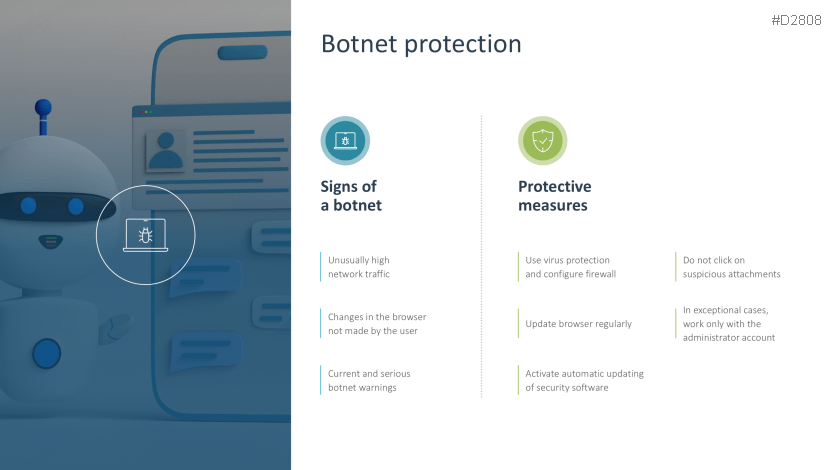
- Botnet protection
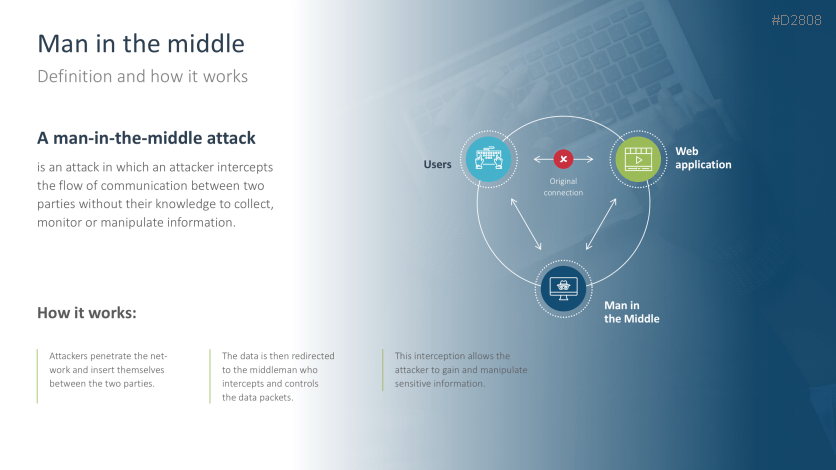
- Man in the Middle
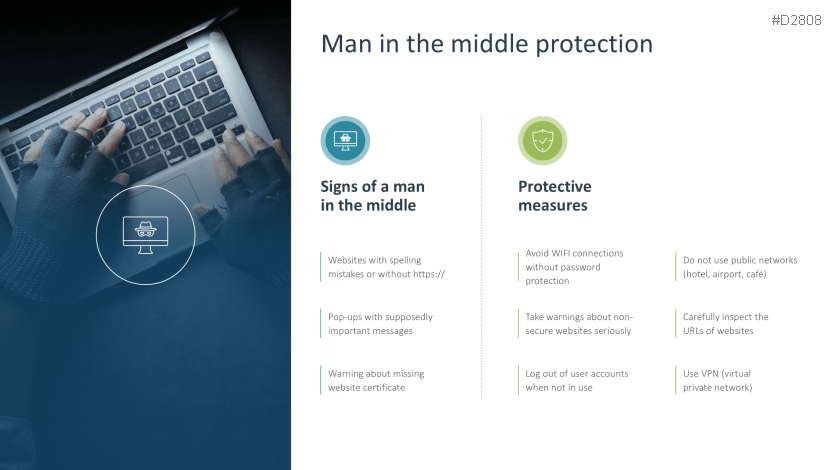
- Man in the Middle protection
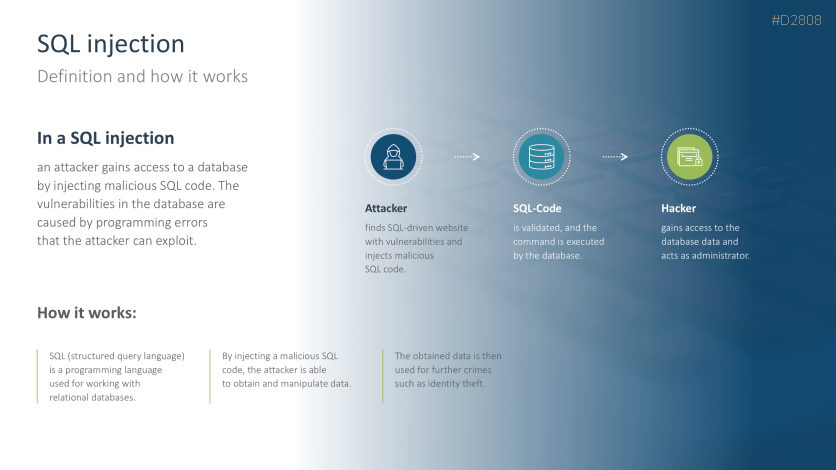
- SQL injection
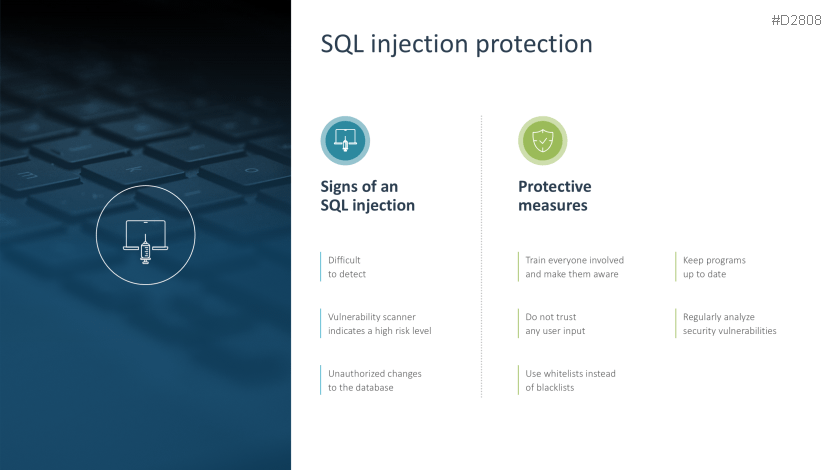
- SQL injection protection
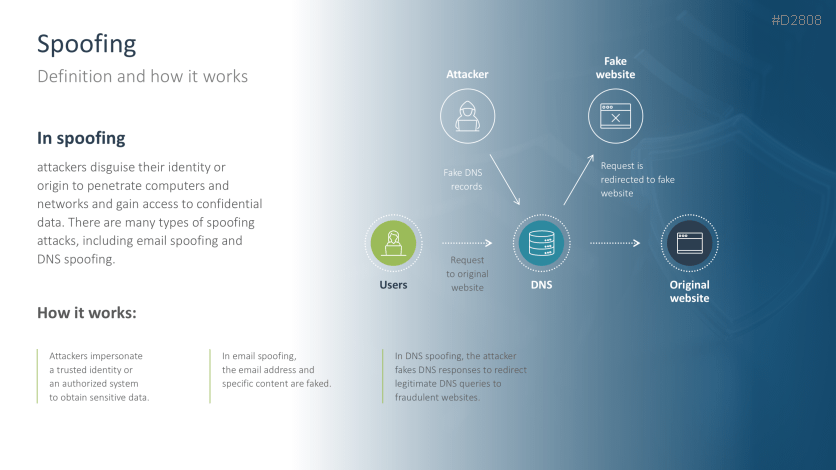
- Spoofing
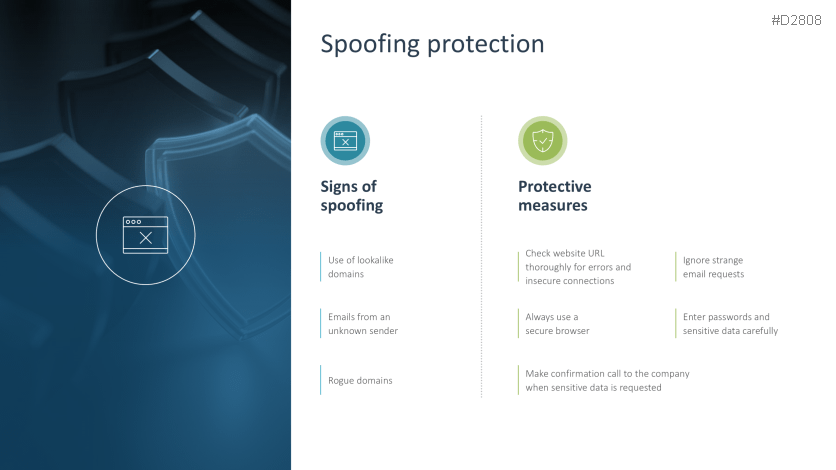
- Spoofing protection
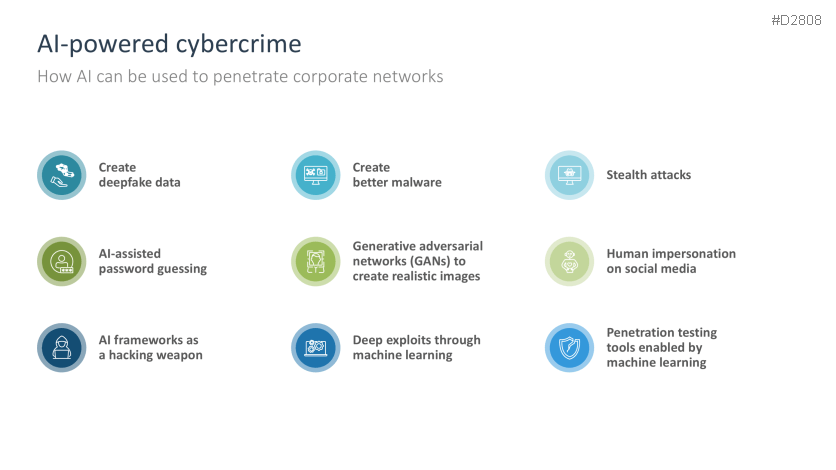
- AI-powered cybercrime
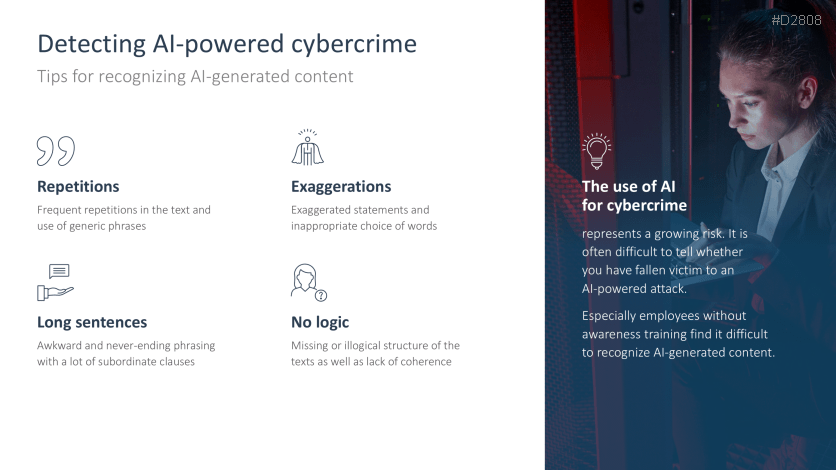
- Detecting AI-powered cybercrime
- Defense strategies and tools
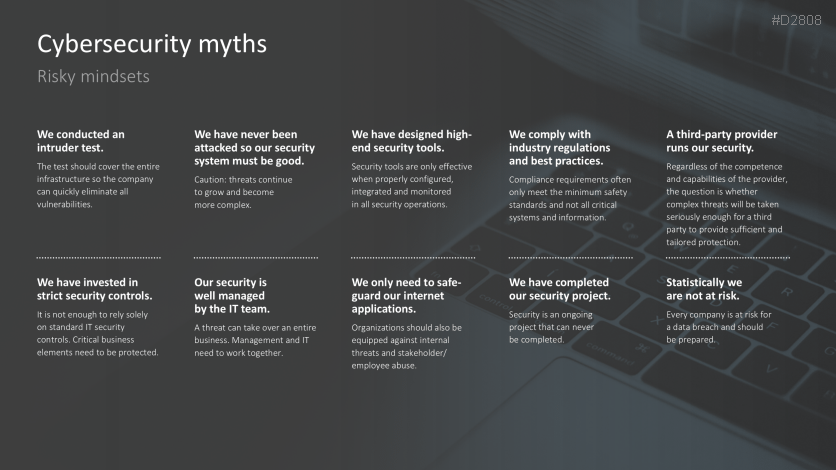
- Myths of cybersecurity
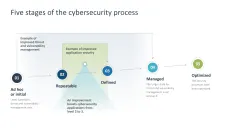
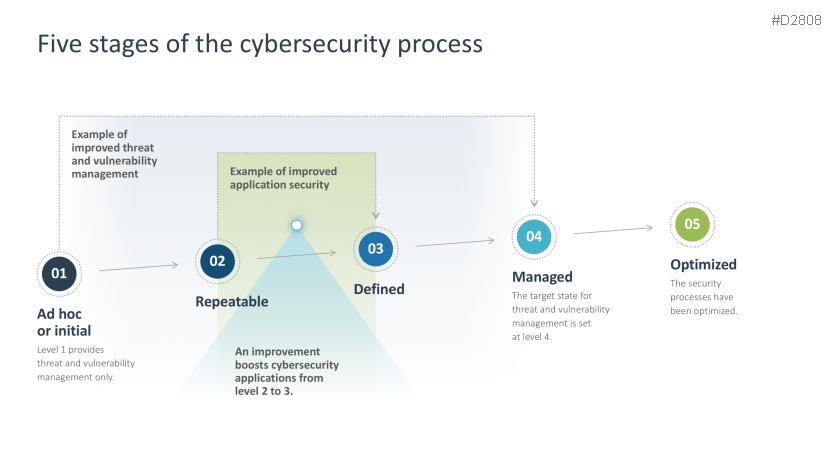
- Five stages of the cybersecurity process
- Different levels of cybersecurity
- Four steps to better cybersecurity
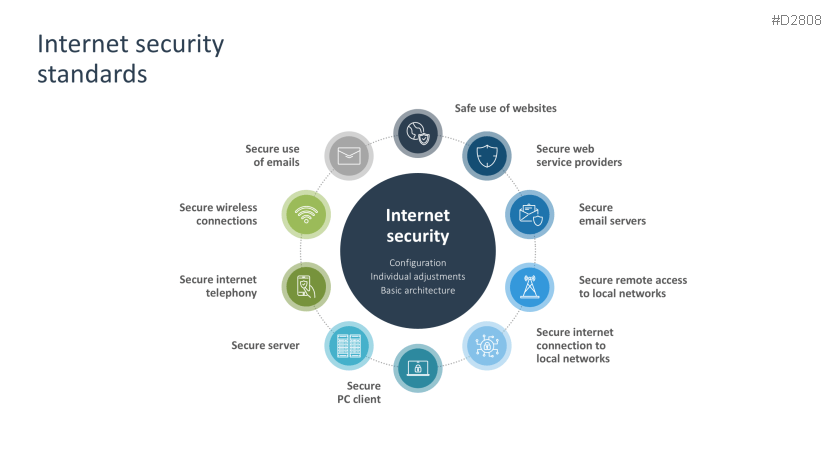
- Internet security standards
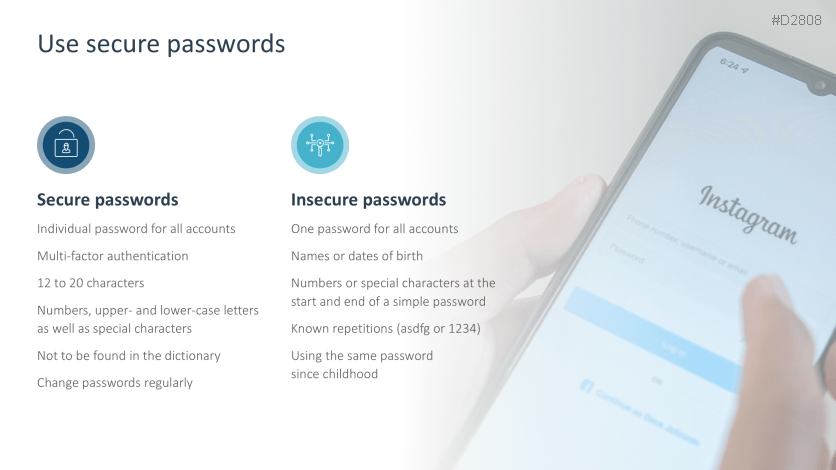
- Using secure passwords
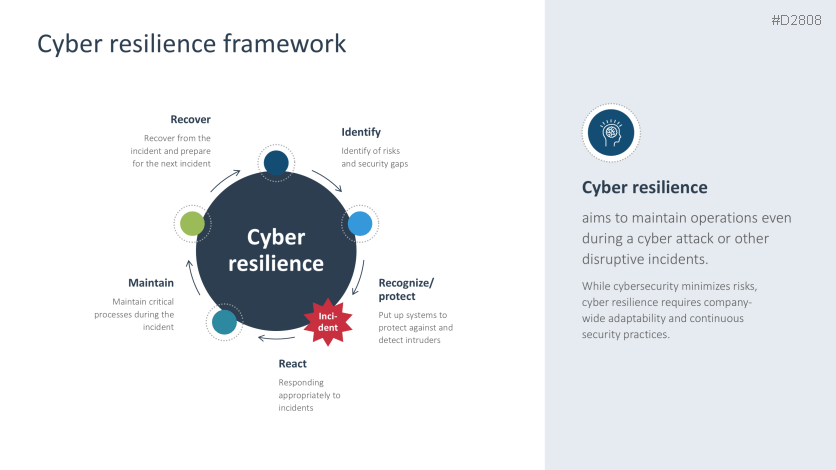
- What is cyber resilience?
- Cyber resilience framework
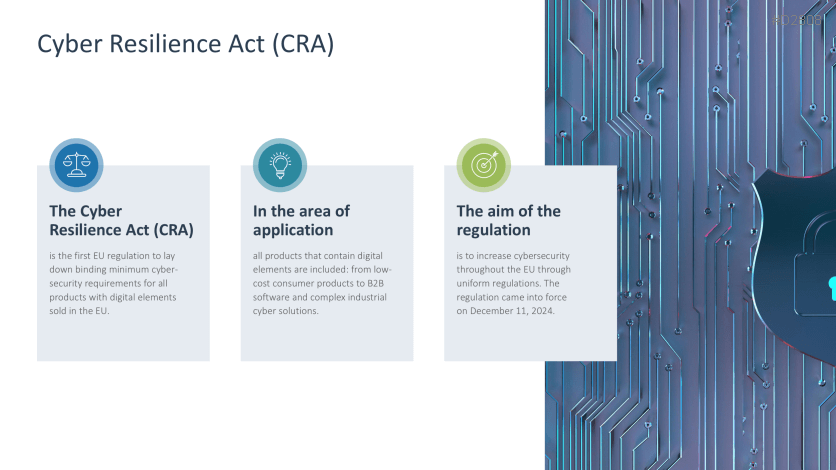
- Cyber Resilience Act (CRA)
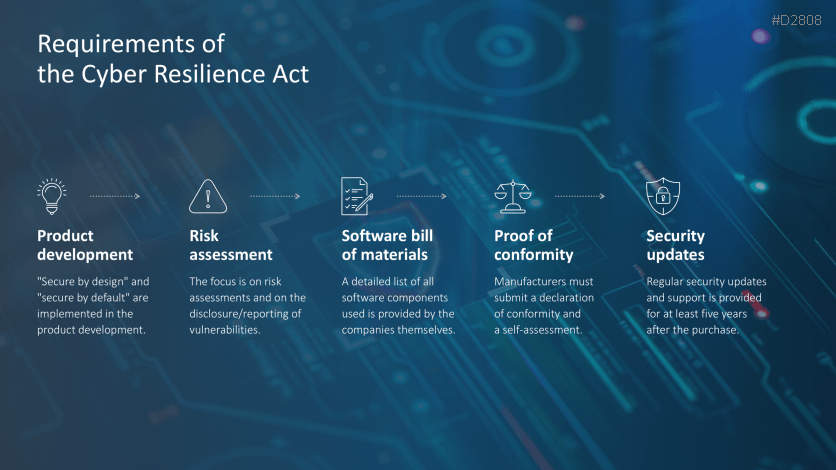
- Requirements of the Cyber Resilience Act
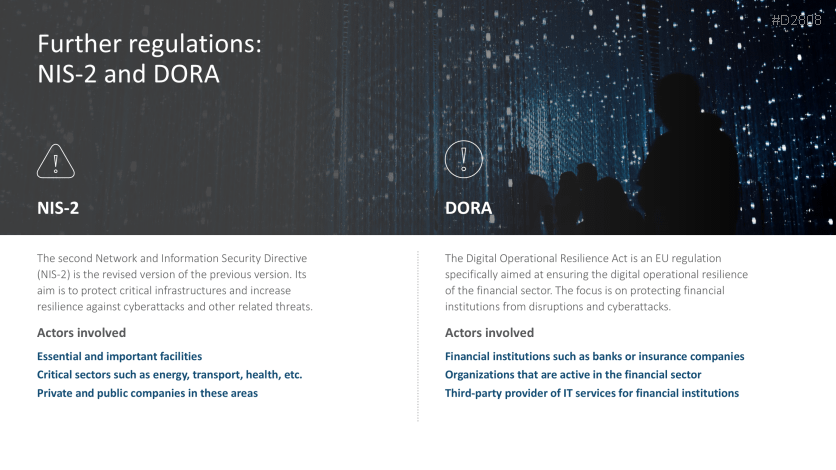
- Further regulations: NIS-2 and DORA
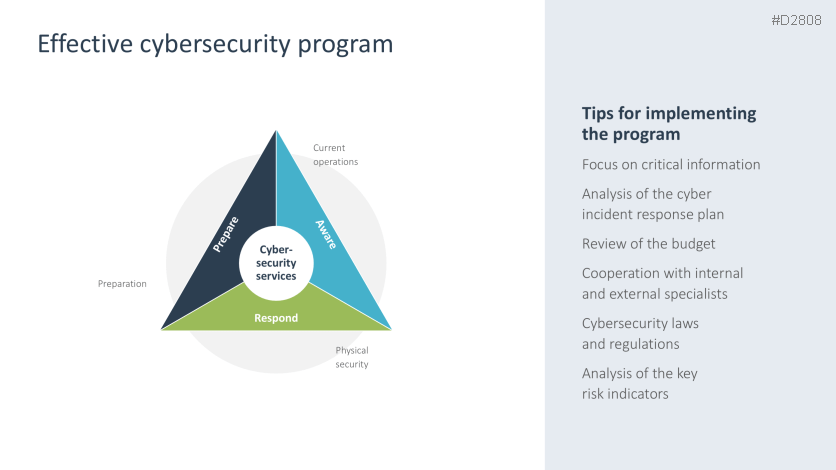
- Effective cybersecurity program
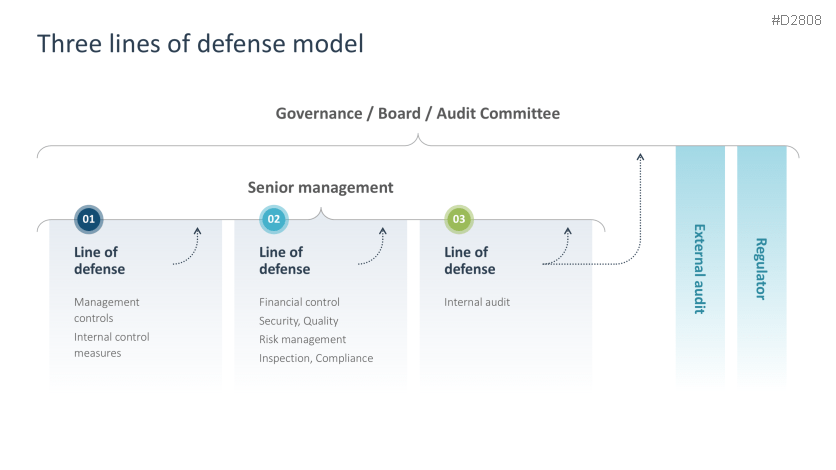
- Three lines of defense model
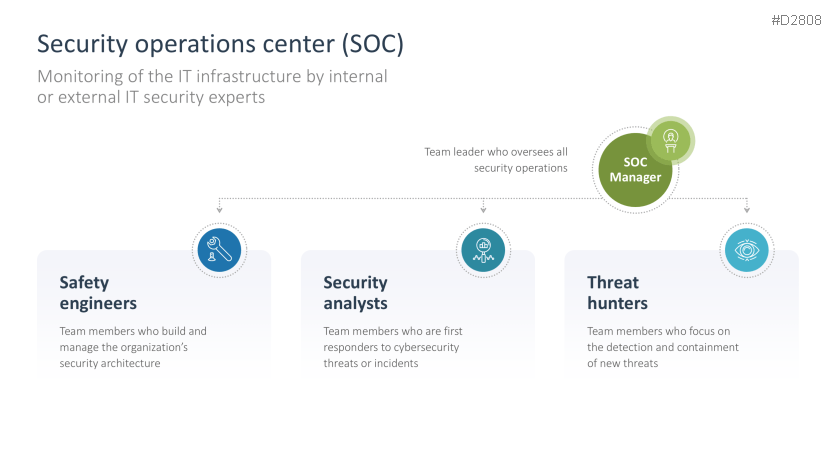
- Security operations center (SOC)
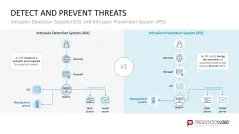
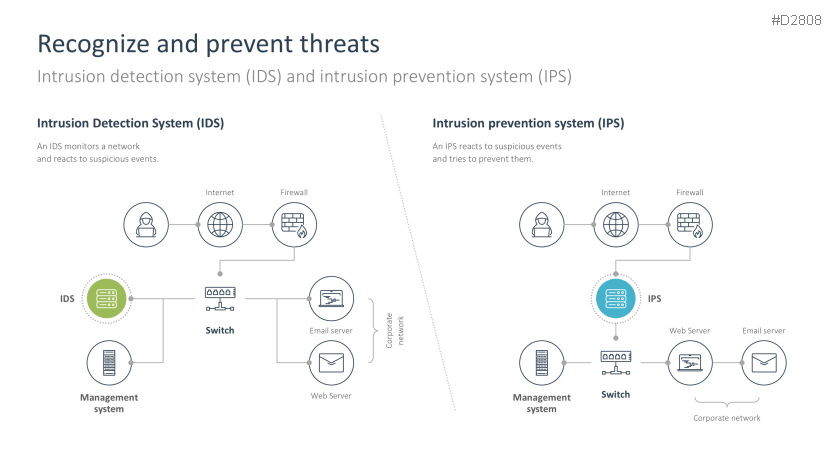
- Intrusion detection system (IDS) vs. Intrusion prevention system (IPS)
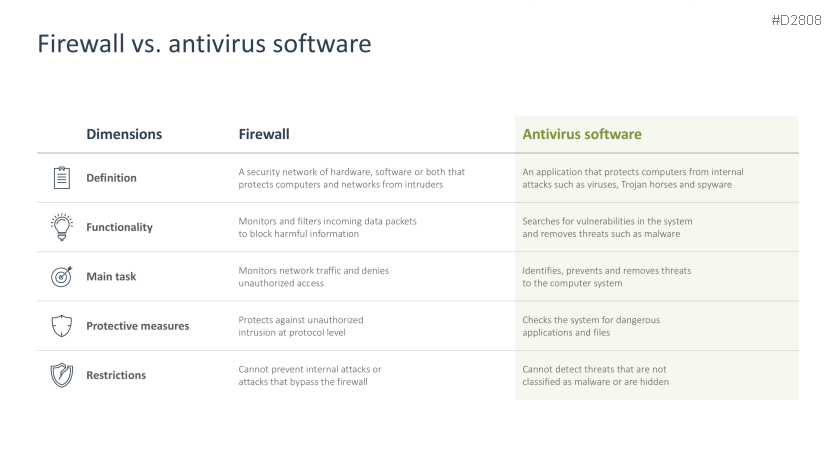
- Firewall vs. antivirus software
- Incident response plan
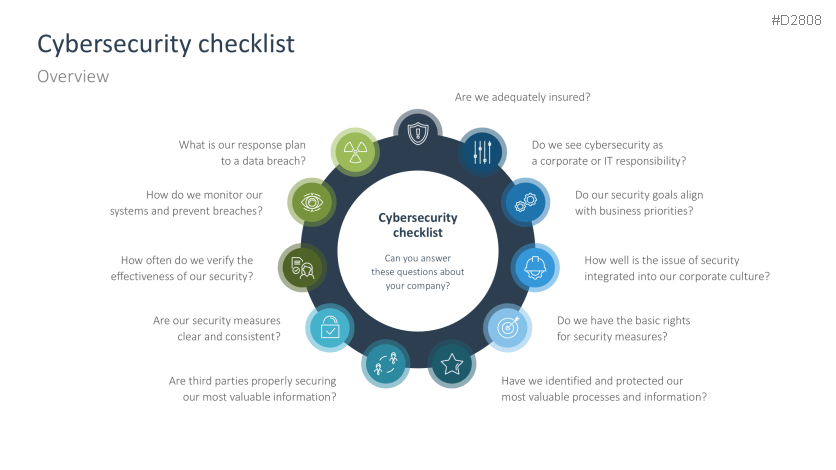
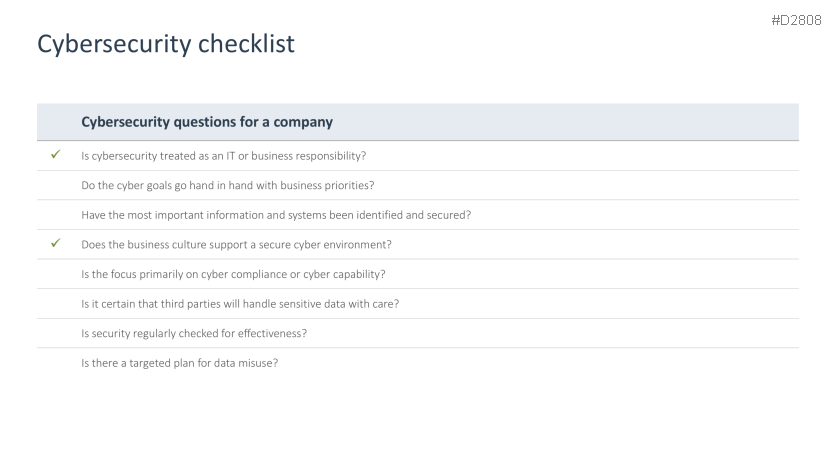
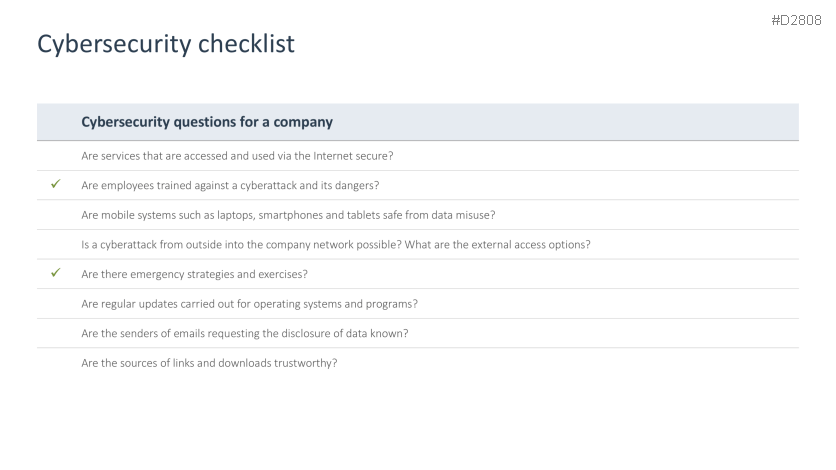
- Cybersecurity checklist
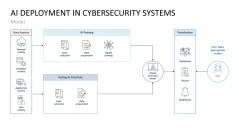
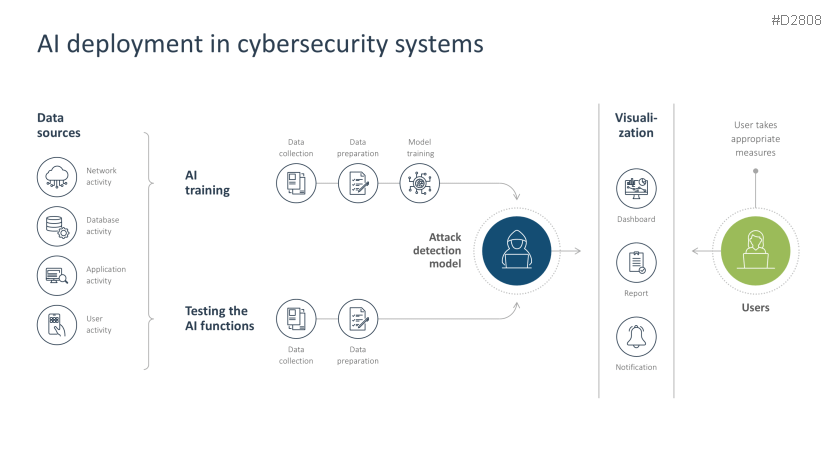
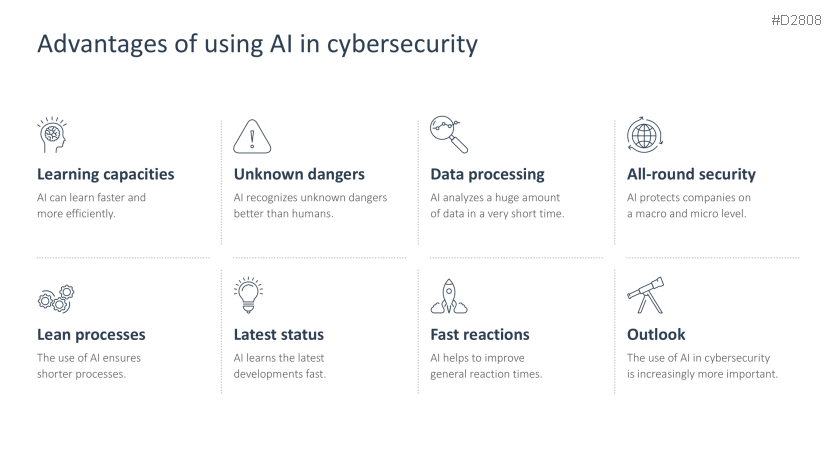
- AI deployment in cybersecurity systems
- Advantages of using AI in cybersecurity